
Do you want to secure your WordPress website? Excelent, in this article, we listed the top 9 common WordPress security vulnerabilities you need to know and how you can prevent them.
Fortunately, many of these WordPress vulnerabilities can be easily prevented or fixed.
WordPress is an incredibly popular open-source CMS (content management system) platform used by over 43% of all websites on the internet. Unfortunately, popularity makes it a prime target for hackers looking to exploit WordPress security vulnerabilities.
It’s essential to stay vigilant and keep up to date with the latest security trends, by following our tips you can significantly reduce the risk of your WordPress site being hacked. So, let’s get started.
Quick Tips: If you don’t want to read the whole WordPress security checklist, you can install Wordfence, Solid Security, or Malcare plugin on your website to secure your website from unwanted visitors.
1: Outdated WordPress Core version
First of all, you should always keep your WordPress version updated. It’s one of the easy ways to prevent security vulnerabilities on your website. WordPress team regularly updates WordPress versions to fix bugs, add new features, and address security vulnerabilities.
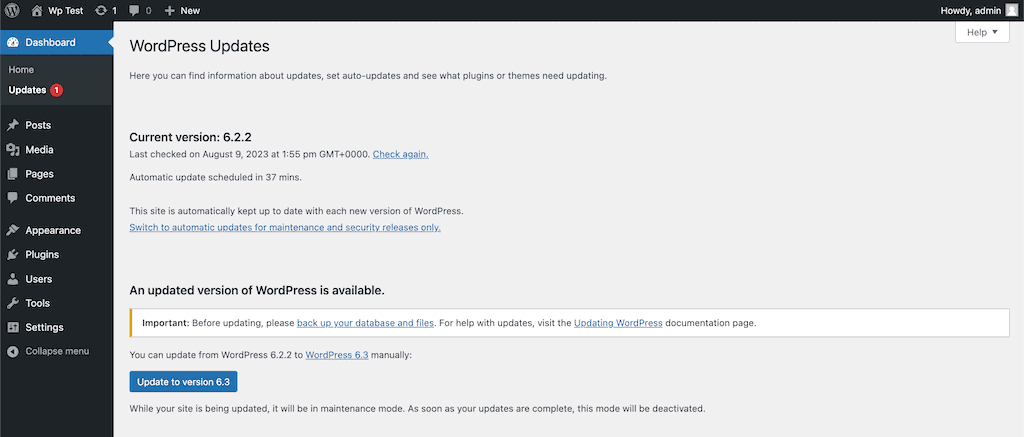
If you are using an older WordPress version on your website, it may be vulnerable to known exploits. Updating the WordPress version is easy and can be done through the WordPress dashboard. You can also enable automatic updates for minor releases, ensuring that your site is always up to date.
Unless you use managed WordPress hosting for major WordPress version releases, you will have to initiate the WordPress update yourself manually.
Quick Tip: Before installing the latest WordPress version on your website, take a complete backup. I recommend you use the UpdraftPlus, Solid Backups, or Blogvault plugin to take a backup.
2: Weak Passwords & 2-Factor Authentication
Using a weak password on your admin login is strongly discouraged as it poses significant security risks to your website. You should always stay away from easily guessable choices like “password,”, “admin”, “123456,” or “qwerty”.
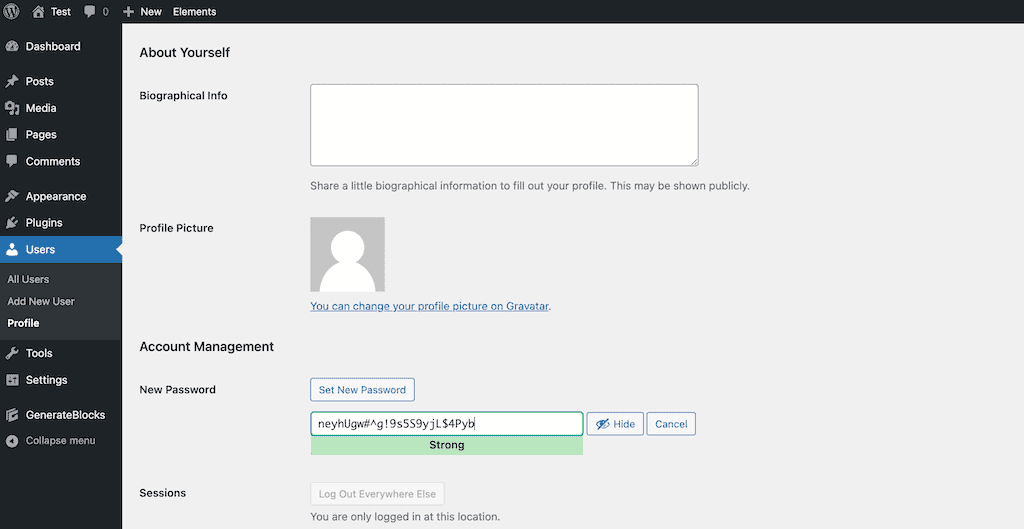
Create your website admin login password with at least 12 characters, combining upper and lower case letters, numbers, and special characters. Most importantly, don’t use the same login passwords on multiple websites. You can use 1Password, LastPass, or Dashlane password managers to generate and store strong passwords securely.
Nowadays, using a strong password is not enough. You’ve to enable two-factor authentication on your WordPress website. It’s just an extra layer of WordPress admin login security, if somehow hackers get to know your password, they still can’t log in without OTP.
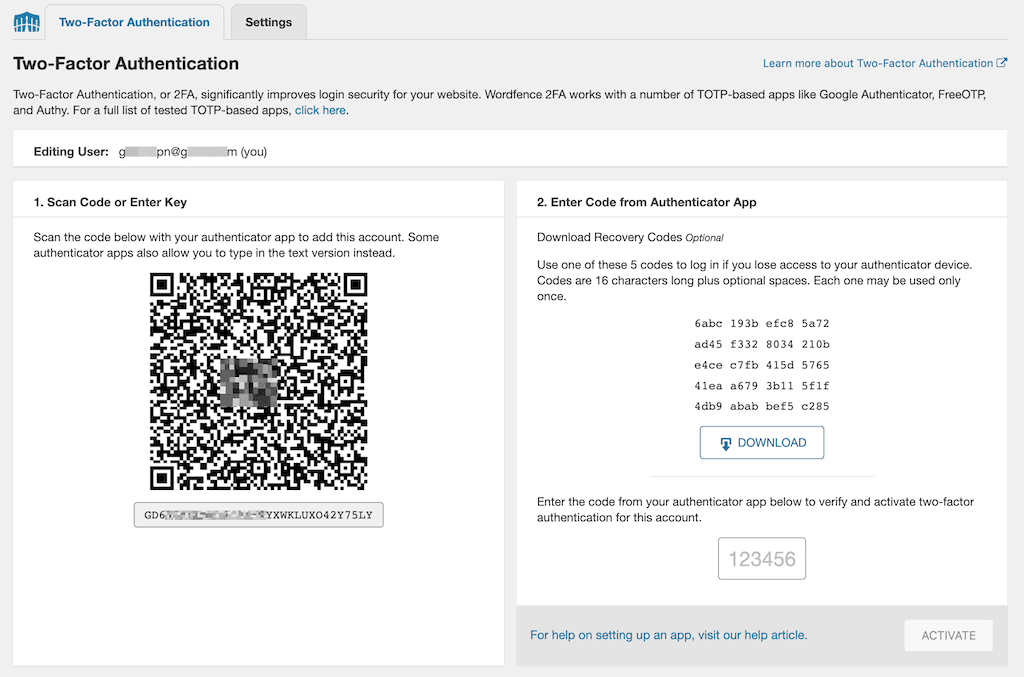
Activating two-factor authentication in your WordPress is really simple; all you have to do is install a plugin. There are plenty of plugins that can help you with things like “Wordfence Login Security”, “Two-Factor”, “Solid Security”, etc.
Note: With the Wordfence Login Security plugin, you can enable Google ReCAPTCHA v3 on your login and registration pages. It helps you stop automated spam, bots from trying to log in multiple times.
4: Insecure Web Hosting
Your hosting provider is responsible for the overall security of your WordPress site. If you’re using a low-quality, cheap hosting server, then your site may be potentially vulnerable to attacks.
To solve this issue, choose a reputable hosting that uses the latest hosting security measures, including SSL certificates, CDN, firewalls, regular backups, etc. There are many hosting providers that offer secure hosting services for WordPress. Right now, I am using Rocket.net to host this website.
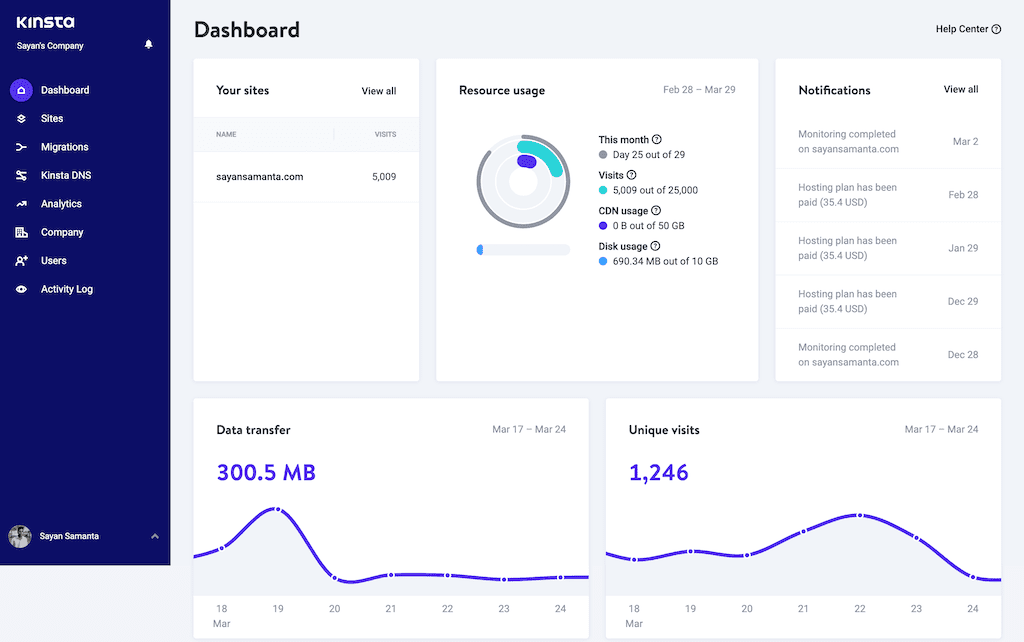
If you are looking for secure WordPress hosting, you can use premium managed WordPress hosting like Kinsta, WPX, WP Engine, CloudWays, or Nexcess, or you can use cheap shared WordPress hosting like A2 hosting, InMotion, or Dreamhost.
4: Using Vulnerable Themes and Plugins
Nulled themes and plugins are pirated copies of premium WordPress products. Hackers can inject malicious code, and it can spread across websites, which makes it difficult to detect and fix.
If you are using Nulled plugins or themes, then stop using them right now. Most of the time, using nulled themes & plugins on your website is the main culprit of being hacked. You can use Sucuri to check whether your website has malicious plugins & themes for free.
Always use trusted and reputable plugins and themes, and keep them updated to their latest versions to avoid being hacked. If you’re using premium themes or plugins, make sure to download them from official websites.
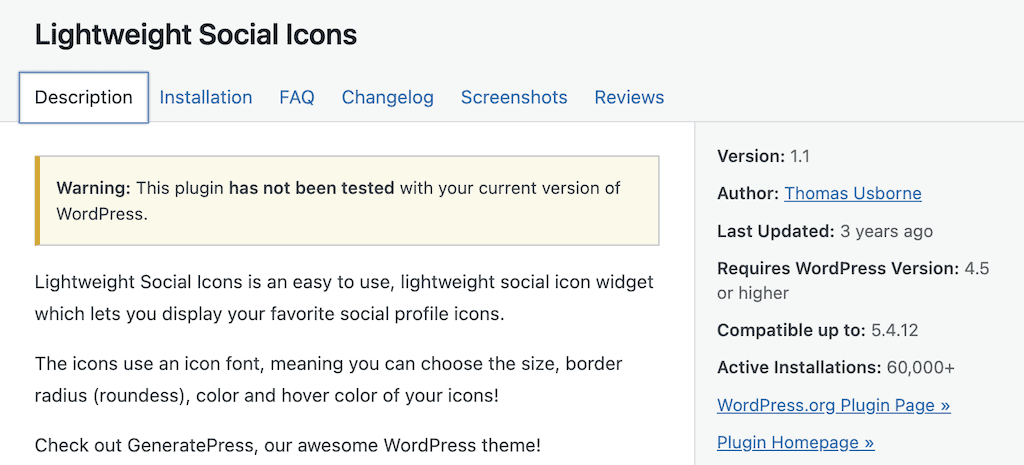
Also, before using any plugin or theme on your website, check reviews and update your history to ensure they are safe and reliable. Try to avoid using outdated plugins, even though they are downloaded from WordPress repositories.
Note: The top three WordPress plugins that hackers exploit are WooCommerce, Yoast SEO, and Gravity Forms.
5: SQL Injection Attacks
An SQL injection vulnerability gives hackers complete access to your WordPress site database through the use of malicious code. According to OWASP, SQL injection is one of the top ten most critical web application security risks.
To protect against SQL injection attacks, you need to use the latest WordPress code version and update PHP, and MySQL. Also, you can Avoid using the root user to connect the SQL database, using pirated WordPress themes, plugins, etc.
I recommend you use a security plugin that provides a firewall to monitor & protect against SQL injection attacks. I recommend using “Wordfence” or “Solid Security” to protect against any type of potential WordPress security vulnerabilities.
6: Cross-Site Scripting (XSS)
Cross-Site Scripting, also known as XSS is a type of WordPress security vulnerability that allows hackers to inject malicious code into your website.
This malicious code is usually in JavaScript, disguised as good code, and very hard to detect. This code can be used to steal data, redirect users to a malicious site, Run web browser-based exploits, or hijack user sessions.
You can protect against XSS attacks by using a good security plugin that provides firewall protection against Cross-Site Scripting (XSS) attacks. I recommend you use Solid Security, Sucuri, or Wordfence security plugins to protect against this type of attack. If you are wondering whether you’ve to XSS vulnerability on your site, you can use the Sucuri site check scan.
7: Brute Force Attacks
Brute force attacks are a common hacking technique that uses trial and error to crack login credentials. It means hackers use automated software to try hundreds or thousands of password combinations in a short time to guess your WordPress admin login details.
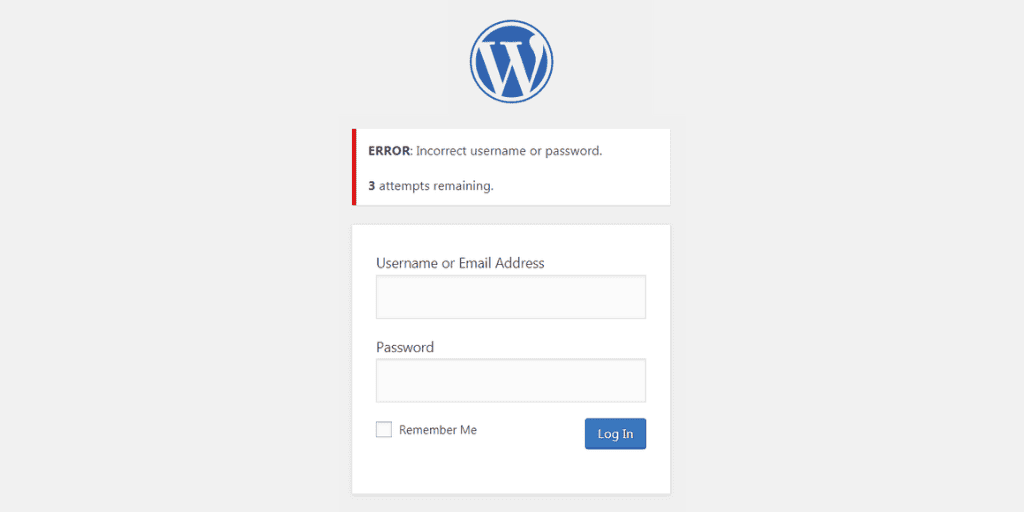
Blocking Brute force attacks is simple on WordPress, all you do is use a strong password and a login protection plugin. WordPress login security plugins can limit the number of login attempts in a certain amount of time. It can also block suspicious IP addresses that fail to login after a certain number of attempts, and provide instant email notifications of any suspicious login attempts.
There are many free WordPress login security plugins available, I use “Limit login attempts” to stop brute force attacks. You can also enable Google reCAPTCHA verification to further improve login security.
8: File Upload Vulnerabilities
In WordPress sites, insecure file upload permissions can also pose a security risk. Setting the correct file permissions is essential to prevent unauthorized access. You can protect against WordPress file upload vulnerabilities by restricting file types and sizes and validating file contents.

You can use a security plugin like the Solid Security or Wordfence plugin that provides firewall protection against file upload attacks, or you can manually set the correct permission levels using an FTP client.
9: Lack of Backups
Yes, lack of backup can be WordPress vulnerabilities & a pretty nasty nightmare too (trust me I’ve been there). If somehow your website is hacked, a backup is the only way to save your years of work. Right now, most of the hosting providers offer regular backups of your WordPress site files, database, etc.
However, hosting backup is not enough, you need to back up your website data regularly. Regular file backups are essential to protect against potential data loss, server failures, and security breaches.
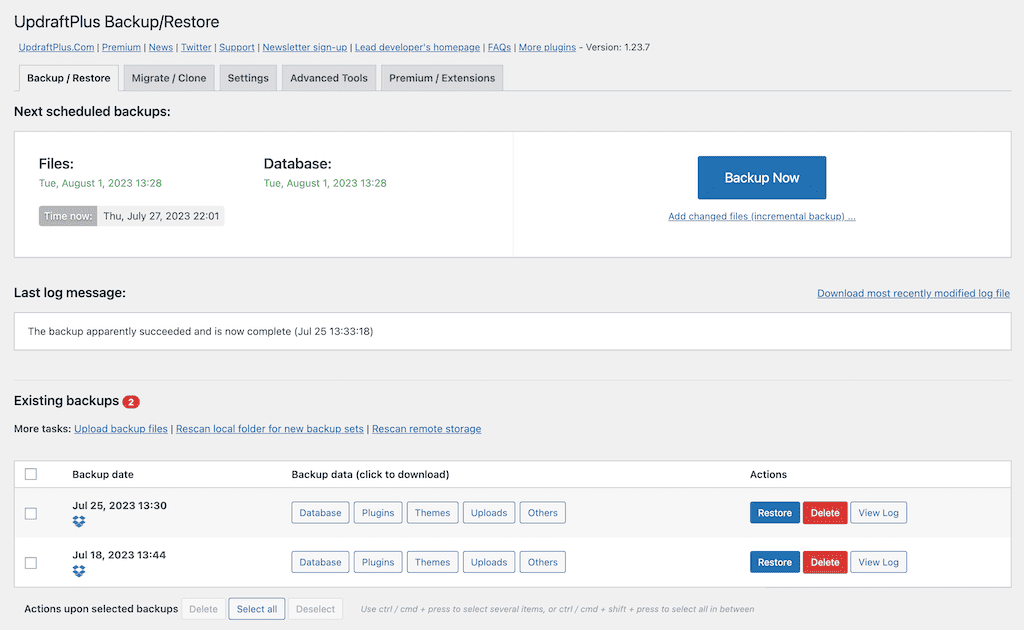
You can use a WordPress plugin like “UpdraftPlus” or “BlogVault” to create a regular backup of your website. and store backups. These plugins are very easy to use and allow you to back up and restore with a single click.
And most importantly, you can save your backup files to remote cloud storage like Google Drive, Dropbox, Amazon S3, etc. I personally prefer to use the UpdraftPlus plugin to create regular backups of my websites.
Final Thoughts on Common WordPress Security Vulnerabilities
It’s important for you to know that even with the best security practices in place, no website is 100% secure. That doesn’t mean you don’t have to take security measures.
It’s essential to regularly monitor your WordPress site for suspicious activity and take immediate action if you notice any potential security issues arise. For more information, I wrote a WordPress security checklist for you to avoid being hacked.
Stay vigilant and keep up to date with the latest security trends and techniques to stay one step ahead of potential attacks against your WordPress site. By staying informed about WordPress vulnerabilities and implementing the best security practices, you can ensure the longevity of your WordPress website.
That’s all for now. If you have any questions regarding WordPress security vulnerabilities, please let me know in the comments section.
Read more about:
- How to reduce server initial response time.
- Best WP Rocket settings for core web vitals.
- WP Rocket cache plugin review.
Thank you. Have a nice day.
